Books in category of Cyber Security
Page of
Explore the World of Cyber Security
In today's technologically driven environment, Cyber Security is a critical field that ensures the safety and integrity of information systems against unauthorized access, attacks, and damages. At Refhub.ir, we offer an extensive collection of Cyber Security books that provide deep insights into this vital sector.
Why Cyber Security Matters?
As our reliance on digital systems increases, the threats associated with cyber attacks also rise exponentially. Cyber Security is crucial for protecting sensitive data ranging from personal information to corporate assets and governmental intelligence. By understanding the intricacies of cyber threats and defense mechanisms, individuals and organizations can safeguard their operations from potential cyber risks.
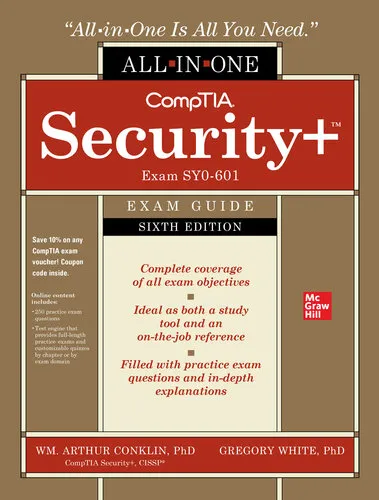
Comprehensive Collection of Books
Our Cyber Security category hosts an array of comprehensive resources catering to varied levels of expertise. Whether you are a beginner exploring the basics or an advanced professional seeking to enhance your knowledge, our curated selection of books covers a broad spectrum of topics. Explore foundational concepts, advanced threat analysis, penetration testing, network security, cryptography, ethical hacking, and much more. Our goal is to equip you with the necessary skills and knowledge to tackle real-world cyber security challenges.
Stay Ahead with Latest Trends and Technologies
In the dynamic field of Cyber Security, staying updated with the latest trends, tools, and technologies is imperative. Our collection is regularly updated to include the latest publications that shed light on emerging trends such as AI and machine learning in cyber security, the role of blockchain technology, and advanced persistent threats (APTs). By keeping abreast of these ongoing developments, you can maintain and enhance your protective strategies effectively.
Understanding Cyber Threats and Defense Mechanisms
Cyber Security is a constantly evolving warfare between malicious actors and defenders. Understanding the nature of various cyber threats, including phishing attacks, malware, ransomware, and DDoS attacks, is crucial for implementing effective defense mechanisms. Our books delve into these threats in detail, exploring the tactics, techniques, and procedures (TTPs) employed by attackers, enabling readers to anticipate and mitigate potential security breaches effectively.
Guidance from Industry Experts
Authors of our Cyber Security books come with vast experience and expertise. They offer practical guidance drawn from their professional journeys, providing readers with tried and tested strategies and real-life case studies. Leveraging this expertise allows you to gain actionable insights and frameworks that are applicable in real-world scenarios, enhancing your problem-solving capabilities and decision-making processes in cyber environments.
Tailored Recommendations for Every Learner
Whether you are a student, IT professional, or a business leader, our collection is tailored to meet diverse learning needs. We offer specialized content recommendations based on your professional goals and existing knowledge levels, ensuring you find the right resources to propel you forward in the cyber security domain.
Enhance Your Skills with Practical Activities
Many books in our Cyber Security category are enriched with practical exercises, lab simulations, and assessment questions, providing an interactive learning experience. These practical activities help reinforce theoretical knowledge and enable you to apply concepts in simulated environments, thus preparing you for real-world applications.
Join the Community of Cyber Security Enthusiasts
Being a part of the Cyber Security community offers you opportunities to connect, share, and grow with like-minded enthusiasts and professionals. Engage in discussions, exchange ideas, and stay informed about the latest updates and job opportunities by immersing yourself in this vibrant community that Refhub.ir actively supports.
Embark on your Cyber Security journey with Refhub.ir and gain the expertise needed to protect digital realms. Browse our extensive selection today and empower yourself with the knowledge that shields the future.